JFrog Security Real Time Posts
Last Updated On 5 Apr, 2026
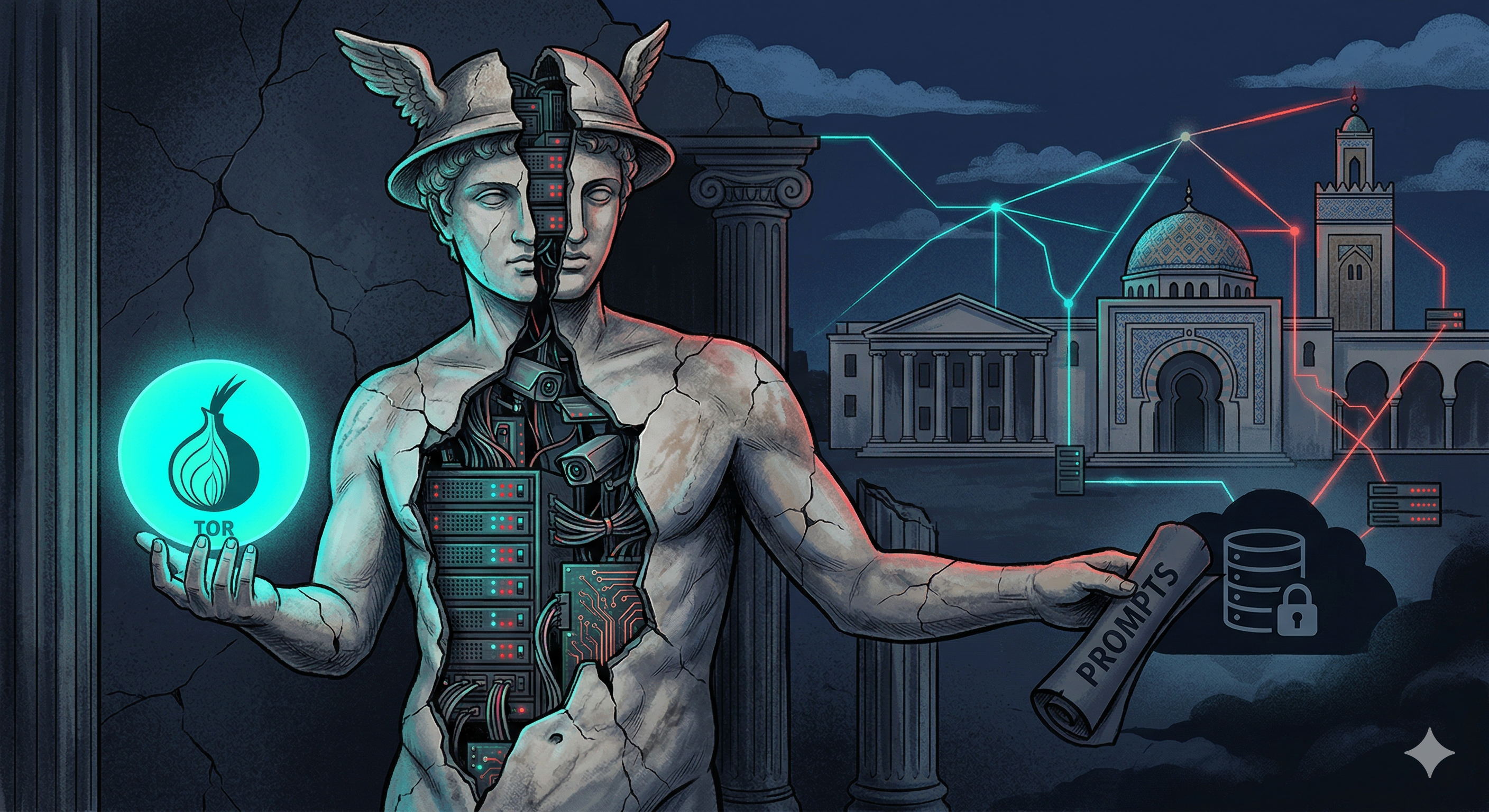
A malicious PyPI package disguised as a Tor-routed AI proxy abuses a Tunisian university's private AI infrastructure, bundles a stolen 246K-character Anthropic Claude system prompt, and silently exfiltrates every user prompt and response to the attacker's Supabase database.
The JFrog security research team recently identified a supply chain attack targeting the `axios` npm package. If you installed `axios@1.14.1`, or `axios@0.30.4` you must assume your environment is compromised.

The JFrog Security research team identified a malicious npm package undicy-http (version 2.0.0) masquerading as the popular undici HTTP client library. Despite its name, the package contains zero HTTP client functionality.

On March 27th, the telnyx popular PyPI library was compromised. new versions of telnyx were uploaded to PyPI, 4.87.1 and 4.87.2. Both contains malicous payload, this compromise is linked to TeamPCP

The JFrog Security Research team has identified that Langflow version 1.8.2, which is widely reported as patched for CVE-2026-33017, remains vulnerable to remote code execution

On March 24th, the litellm popular PyPI library was compromised. new versions of litellm were uploaded to PyPI, 1.82.7 and 1.82.8. Both contains malicous payload, this compromise is linked to TeamPCP

JFrog Security researchers have identified new, previously unreported compromised package versions related to the CanisterWorm npm supply chain attack.

The JFrog security research team recently encountered 2 malicious packages on the NPM ecosystem, delivering via Dropbox links a windows executable. While checking these files in VirusTotal shows almost no Anti Virus (AV) results that flag it, the behavior analysis showed suspicious activity, leading us to dive in.

The JFrog Security research team has identified a malicious npm package named @openclaw-ai/openclawai. This package masquerades as a legitimate CLI tool called "OpenClaw Installer" while deploying a multi-stage infection chain that steals system credentials, browser data, crypto wallets, SSH keys, Apple Keychain databases, iMessage history, and more
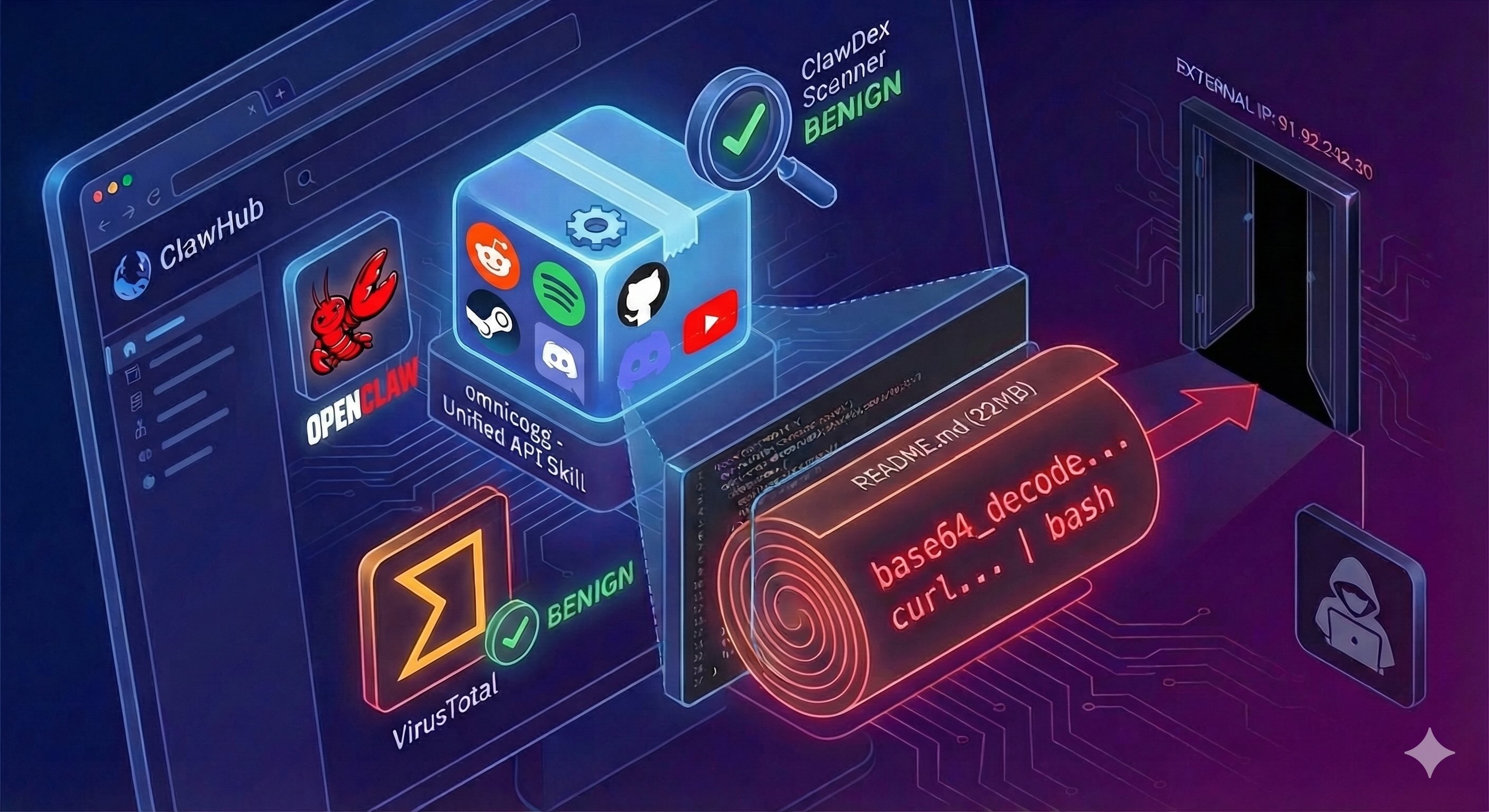
The JFrog Security Team has identified a malicious OpenClaw skill named omnicogg hosted on ClawHub that uses a 22MB padded README to hide a base64-encoded RCE dropper, bypassing VirusTotal, ClawDex, and ClawHub's own scanner to harvest developer credentials.