TL;DR
- Langflow CVE-2026-33017 is actively exploited and listed in CISA KEV
- Public sources claim the latest version, 1.8.2, is patched
- In reality, the vulnerability is still exploitable in 1.8.2
- Actual fixed version (1.9.0) is not yet available
- This was verified using a public PoC, on both the langflow PyPI package and official Docker image
- This creates a dangerous gap between perceived security and actual security
- JFrog alerted the maintainers, which fixed the affected versions in GitHub Advisory Database
The JFrog Security Research team has identified that Langflow version 1.8.2, which is widely reported as patched for CVE-2026-33017, remains vulnerable to remote code execution, creating a dangerous gap between perceived and actual security. We would like to thank the Langflow maintainers for very quickly fixing the range of affected versions after our disclosure to them.
CVE-2026-33017 is a remote code execution vulnerability with a CVSS score of 9.8 (Critical), and its inclusion in the CISA KEV confirms that it is actively exploited in the wild.
The issue stems from unsafe handling of user-controlled input in the build_public_tmp endpoint, where user input is executed within a Python context without sufficient sanitization or validation. This allows attackers to inject and execute arbitrary code on the server.
Successful exploitation allows unauthenticated attackers to:
- Execute arbitrary code on the server
- Access sensitive data
- Pivot to compromise additional infrastructure
Because Langflow is often deployed in cloud and containerized environments such as AWS EC2 and Kubernetes, the real-world impact of this vulnerability is significant and extends beyond a single service into broader infrastructure risk.
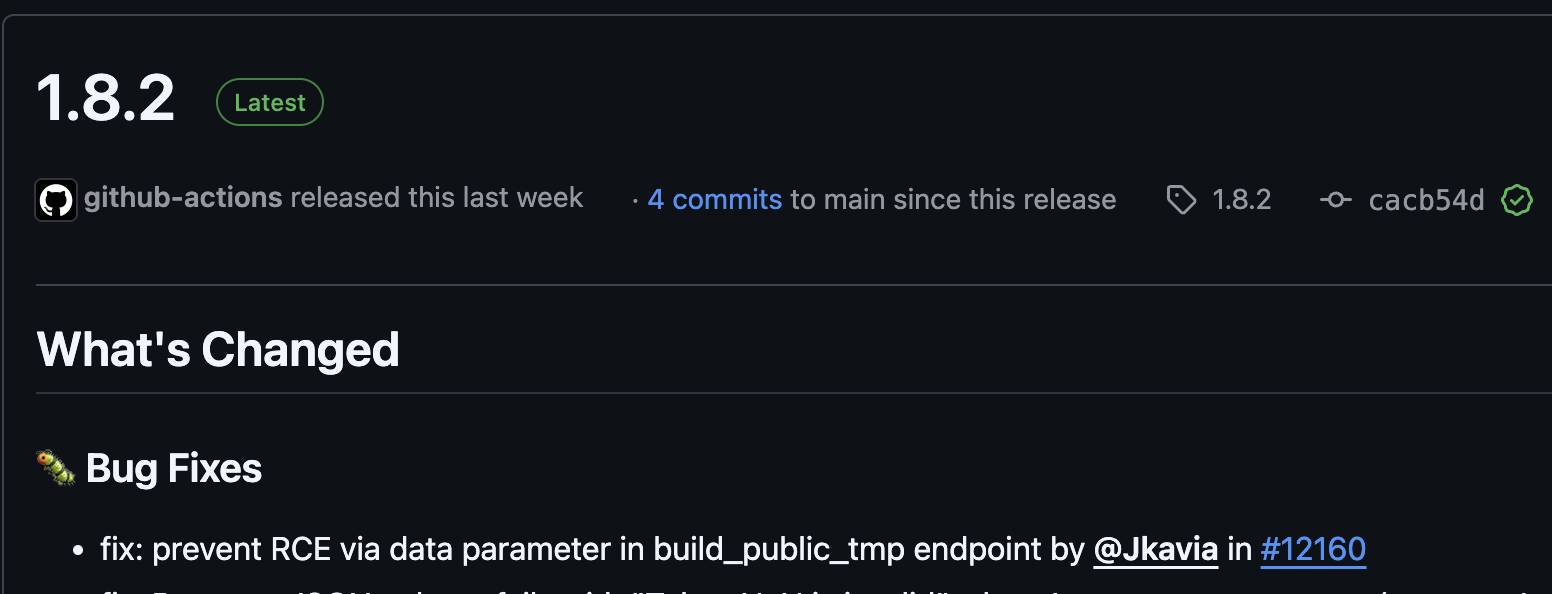
While version 1.8.2 is currently the latest official release of Langflow, the changelog gives the impression that this vulnerability has been fixed in that version.
As shown below, the release notes explicitly mention a fix for the RCE vulnerability:
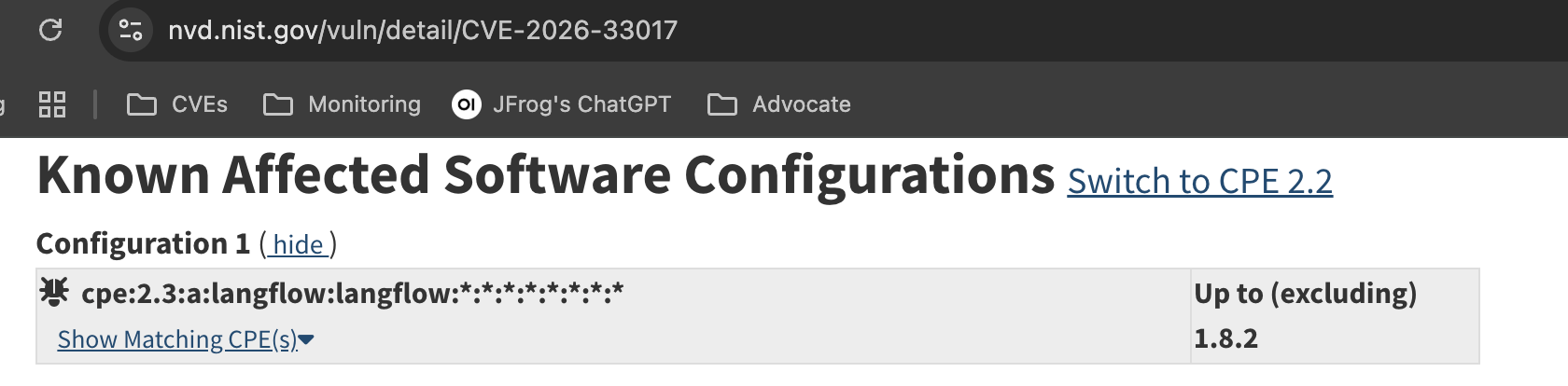
In addition to the maintainer’s statement, multiple external sources also report that version 1.8.2 is patched. For example, the National Vulnerability Database indicates that all versions except 1.8.2 are vulnerable:
Similarly, the GitHub advisory system reports that version 1.8.2 includes the fix:
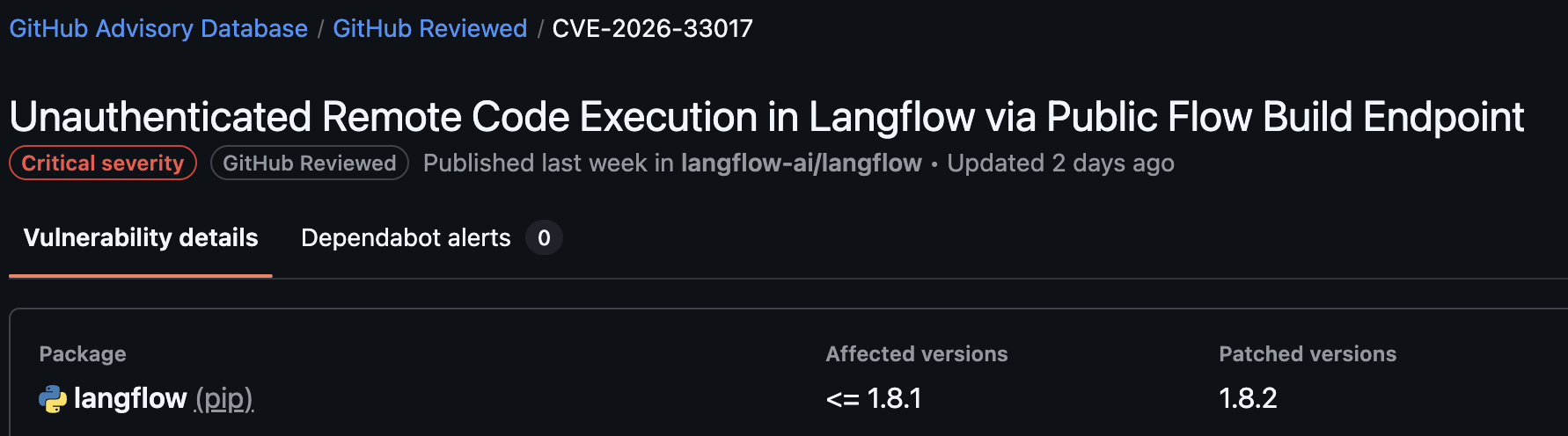
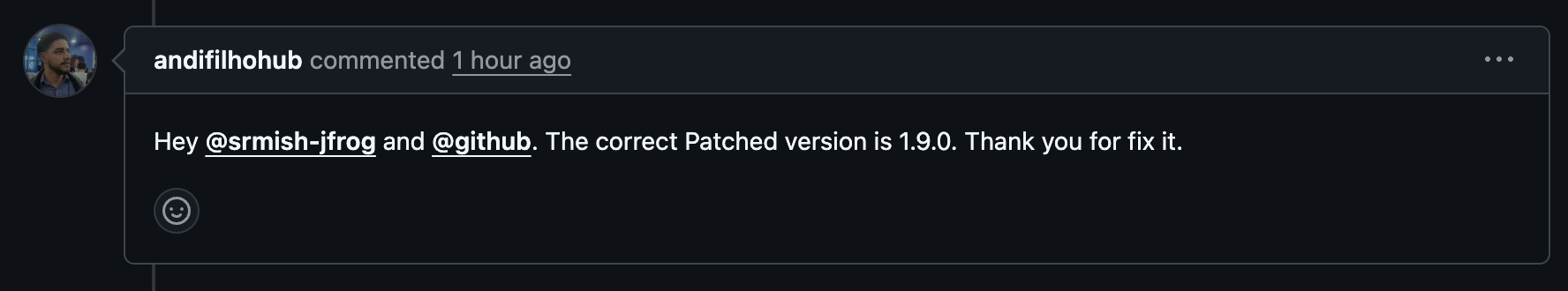
However, at the same time, the maintainer's GitHub advisory, states that patched versions are 1.9.0 and above, even though version 1.9.0 has not been officially released.

This contradiction creates significant confusion for Langflow users, who are left trying to determine which source to trust.
The confusion is further demonstrated by the following issue, that was opened yesterday where users explicitly requested a Docker image for version 1.8.2 so they could upgrade to what they believed was a safe version:
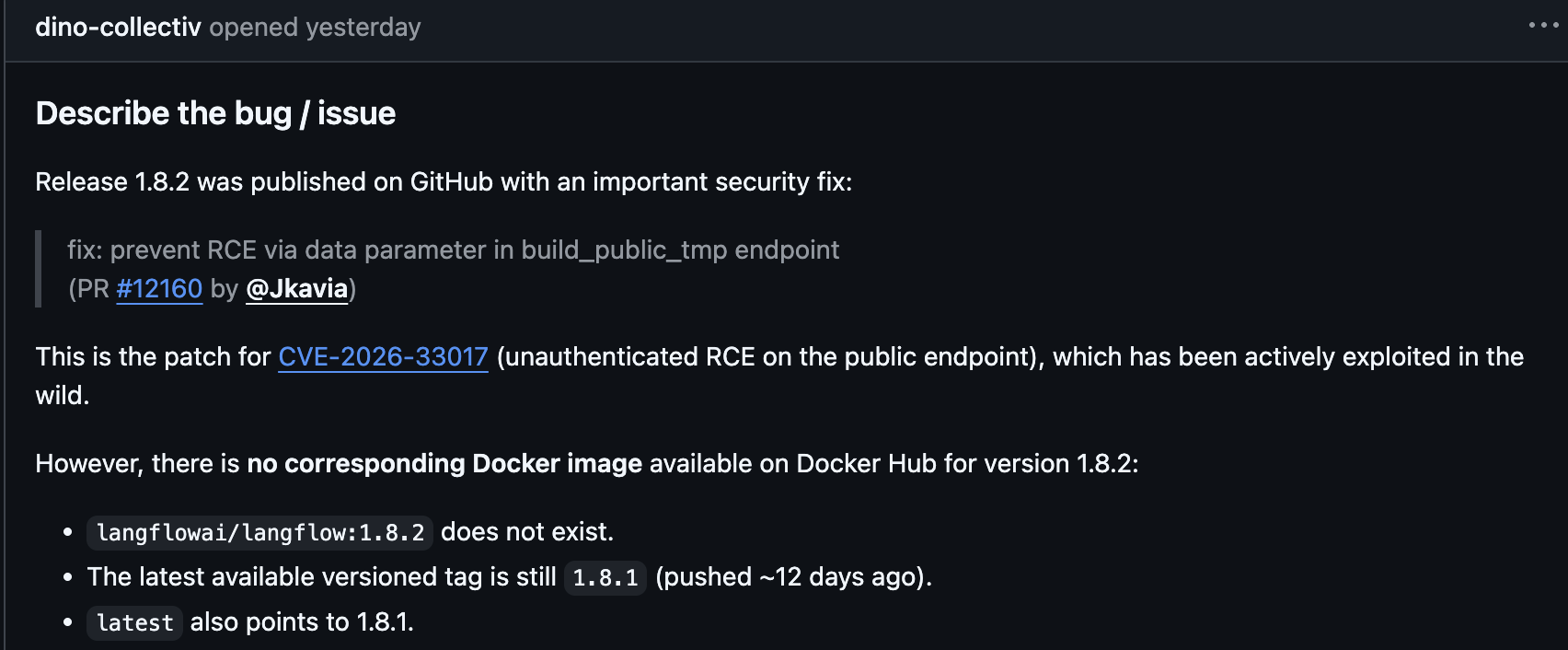
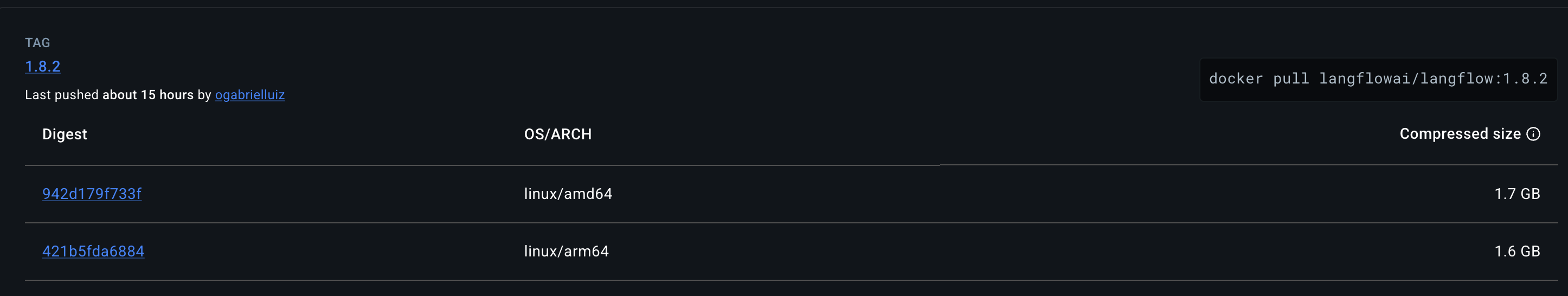
Shortly after, a Docker image for version 1.8.2 was released, reinforcing the assumption that this version is secure and ready for production use.
These inconsistencies led us to a straightforward but critical question: where is the actual fix?
After reviewing the commits of version 1.8.2, we were unable to identify the patch that supposedly addressed the vulnerability. This led us to validate the fix empirically by testing the publicly available PoC:
We executed the PoC against Langflow version 1.8.2 in both PyPI and Docker environments.
As shown below, the exploit successfully triggers remote code execution:
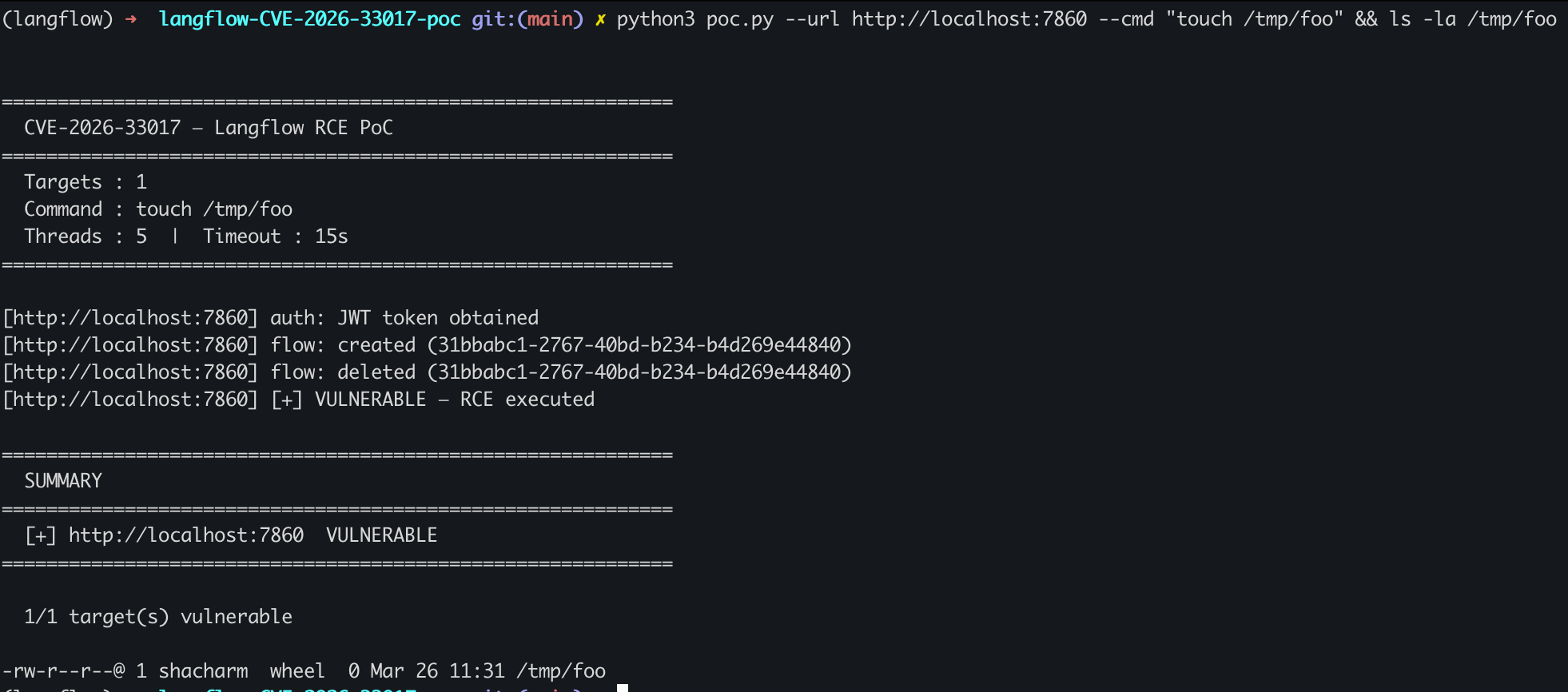
This confirms that version 1.8.2 is still vulnerable.
Both installation methods, PyPI and Docker, resulted in successful exploitation, clearly demonstrating that the vulnerability is not fixed in this version.
After opening an issue and pr to LangFlow with all details, it was confirmed that version 1.9.0 is the correct patched version, which means 1.8.2 is indeed vulnerable.
All official released versions are affected.
- 1.9.0 (to be released) includes a patch.
All official released versions are affected.
- 0.9.0 (to be released) includes a patch.
At the moment, since there is no official LangFlow patched version released, we recommend uninstalling LangFlow and installing langflow-nightly instead.
Our testing shows that the mitigation implemented in langflow-nightly 1.9.0.dev18 is effective, with the PoC failing to achieve code execution.
pip uninstall langflow
pip install langflow-nightly
The case of CVE-2026-33017 in Langflow highlights a fundamental truth in modern software security: security cannot be determined solely by what external sources claim, but only by verifying how the code behaves in practice. This incident reinforces the importance of independent validation and dedicated security research in ensuring that “fixed” truly means fixed.