JFrog Security Real Time Posts
Last Updated On 3 Jun, 2026
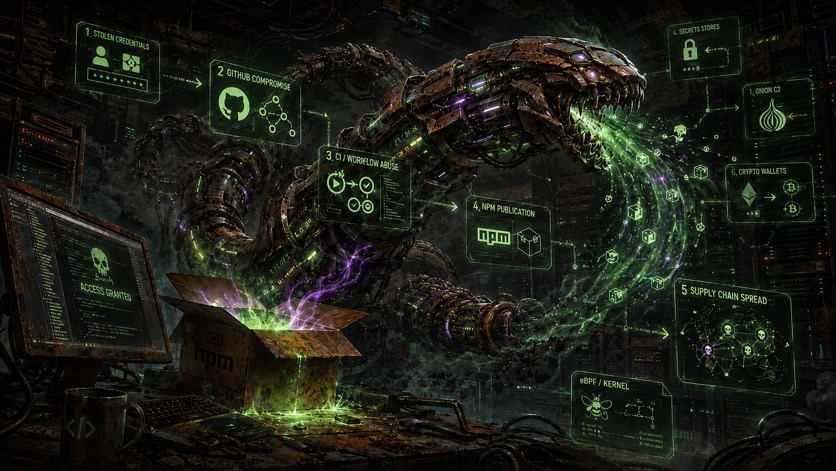
In this article we present research on a malicious npm package that led us to IronWorm: a Rust-built infostealer that scrapes secrets from developer machines, hides behind an eBPF kernel rootkit, and uses Tor for C2. Like Shai-Hulud, it turns stolen credentials into a propagation mechanism, committing itself into victims' GitHub repositories and publishing to the NPM registry.

JFrog Security Research analyzed 31 hijacked `@redhat-cloud-services` npm package versions carrying a new Shai-Hulud variant. The campaign, identified in the payload as "Miasma: The Spreading Blight", uses install-time execution, layered JavaScript obfuscation, Bun-based payload delivery, credential theft, GitHub and npm propagation, and destructive persistence.

JFrog Security Research analyzed the May 19 Shai-Hulud wave across npm and PyPI, where compromised packages used install-time and import-time execution, encrypted credential theft, GitHub dead-drop exfiltration, AI-tool persistence, npm OIDC abuse, lateral movement through AWS SSM and Kubernetes, and an evolved dead-man switch.

The JFrog Security Research team analyzed the Shai-Hulud: Here We Go Again package compromise spanning npm and PyPI, combining CI/CD credential theft, encrypted exfiltration, persistence, worm-like package propagation, and an updated PyPI credentials stealer.

New versions of the malicious npm package `js-logger-pack`, including `1.1.27`, have shifted exfiltration to Hugging Face. Earlier versions already used the platform as a malware CDN; SafeDep documented that earlier phase. What is new is that the operator now outsources stolen data storage to private Hugging Face datasets rather than hosting it on the C2 server directly.

JFrog security researchers identified a hijacked npm package published as @bitwarden/cli version 2026.4.0, impersonating the legitimate Bitwarden command line client.

The JFrog security research team recently identified a supply chain attack targeting the `xinference` package on PyPI. Versions 2.6.0, 2.6.1, and 2.6.2 were compromised and yanked by maintainers after users reported suspicious behavior. If you installed or imported these versions, you must assume your environment is compromised.

JFrog Security researchers have discovered a multi-vector malware campaign distributing the XWorm RAT through both npm packages and a fake game website, targeting Discord users with social engineering tactics.
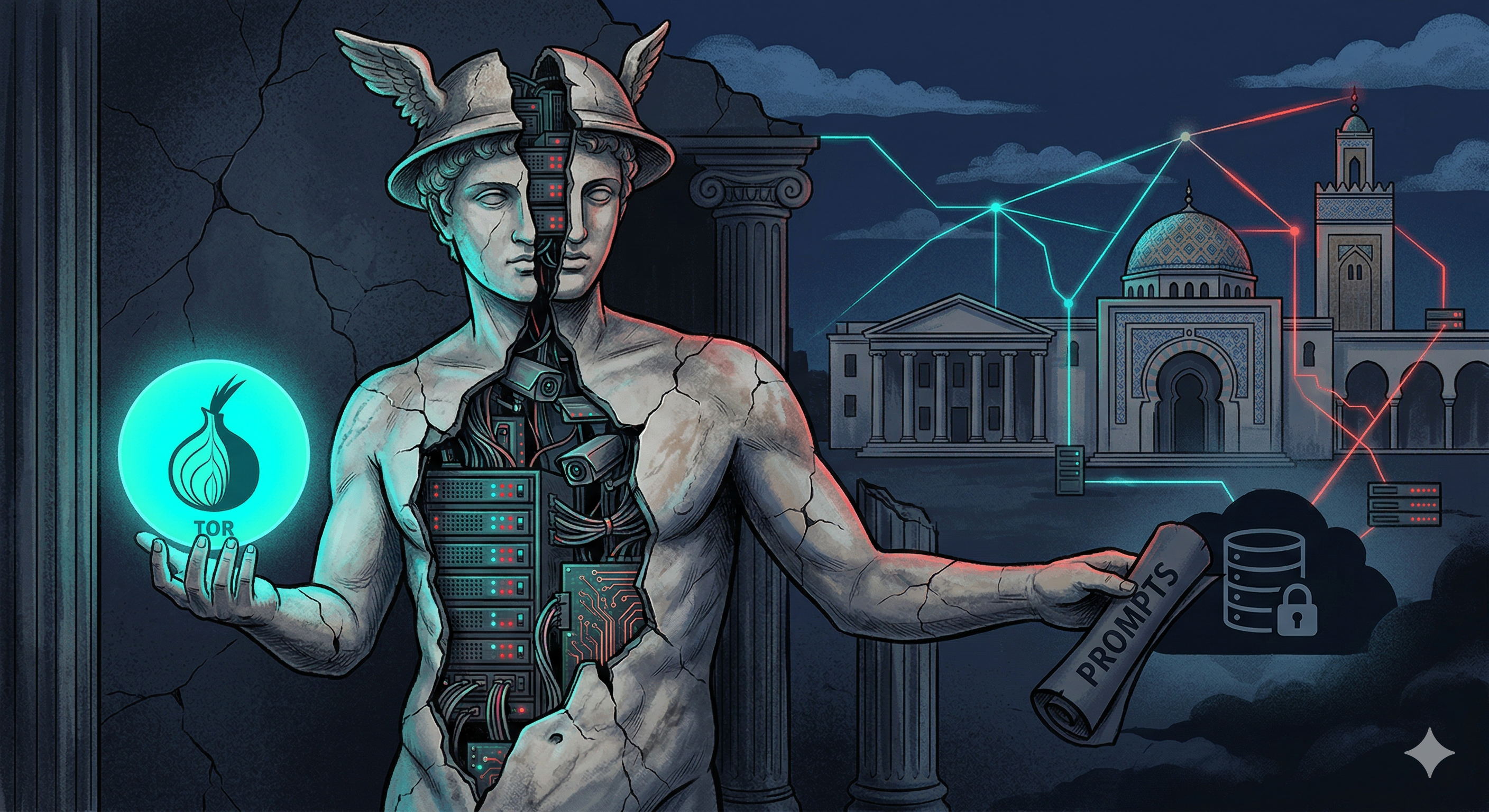
A malicious PyPI package disguised as a Tor-routed AI proxy abuses a Tunisian university's private AI infrastructure, bundles a stolen 246K-character Anthropic Claude system prompt, and silently exfiltrates every user prompt and response to the attacker's Supabase database.
The JFrog security research team recently identified a supply chain attack targeting the `axios` npm package. If you installed `axios@1.14.1`, or `axios@0.30.4` you must assume your environment is compromised.